Extended Reality
The Evolution of XR: From Sci-Fi Dreams to Digital Reality
 Quest Lab Team
Quest Lab Team
You know that moment when you try something for the first time and it completely changes your perspective? That's exactly what happened to me in 1995 when I first experienced a primitive VR system at a computer science exhibition. I was just a wide-eyed teenager then, but that clunky headset showing basic wireframe graphics set me on a path that would define my career in extended reality.
The Sword of Damocles: Where It All Began
Let me take you back to 1968. While most of the world was grooving to the Beatles and watching the space race unfold, a brilliant computer scientist named Ivan Sutherland was crafting something revolutionary in his lab. He called it the 'Sword of Damocles' - not because it was threatening, but because the head-mounted display literally hung from the ceiling like a sword, suspended over the user's head!
"The ultimate display would be a room within which the computer can control the existence of matter." - Ivan Sutherland, 1965
I remember sharing this quote during my first tech conference presentation, and someone in the audience laughed, calling it science fiction. Well, looking at today's mixed reality environments, who's laughing now?
The Virtual Reality Boom and Bust of the 90s
The 1990s were wild times for VR enthusiasts. I still have a yellowing Nintendo Virtual Boy collecting dust in my garage - a testament to both ambition and premature technology. It gave me horrible headaches, but I couldn't stop playing Tennis, even though everything was in headache-inducing red monochrome.
Learning from the Past
The 90s VR boom taught us crucial lessons:
- Technology needs to mature before mass adoption
- User comfort is non-negotiable
- Content is just as important as hardware
- Price points must align with consumer expectations
The Quiet Revolution: Mobile AR Changes Everything
While everyone was focused on VR headsets, something unexpected happened. Pokémon GO launched in 2016, and suddenly my morning commute was filled with people hunting virtual creatures in the real world. It wasn't just a game; it was proof that AR could reach millions without specialized hardware.
I was consulting for a retail company at the time, and the success of Pokémon GO completely changed our AR strategy. Within months, we shifted from developing an expensive VR showroom to creating AR apps that let customers visualize furniture in their homes.
The Meta Effect: Social XR Takes Center Stage
When Facebook rebranded to Meta in 2021, my inbox exploded with messages from old colleagues asking if XR was finally 'ready.' The truth is, it had been ready - we just needed a catalyst to push it into mainstream consciousness.
"The metaverse won't be created by one company. It will be built by creators and developers making new experiences and digital items that are interoperable." - Mark Zuckerberg, Meta Connect 2021
The Enterprise Revolution: XR Means Business
Here's something most people don't realize: while consumers were debating the merit of VR gaming, businesses were quietly revolutionizing their operations with XR. I witnessed this firsthand while working with an aerospace manufacturer in 2022.
- Boeing: Reduced wiring assembly time by 25% using AR glasses
- Walmart: Trained over 1 million employees using VR
- Mayo Clinic: Performing complex surgical planning with mixed reality
- NASA: Using mixed reality for spacecraft design and astronaut training
The Present and Near Future: Where Are We Now?
Just last month, I tried the latest mixed reality headset, and I couldn't help but smile thinking about that wireframe display from 1995. The resolution is crystal clear, the field of view is wide, and the hand tracking is precise enough to let me play virtual piano.
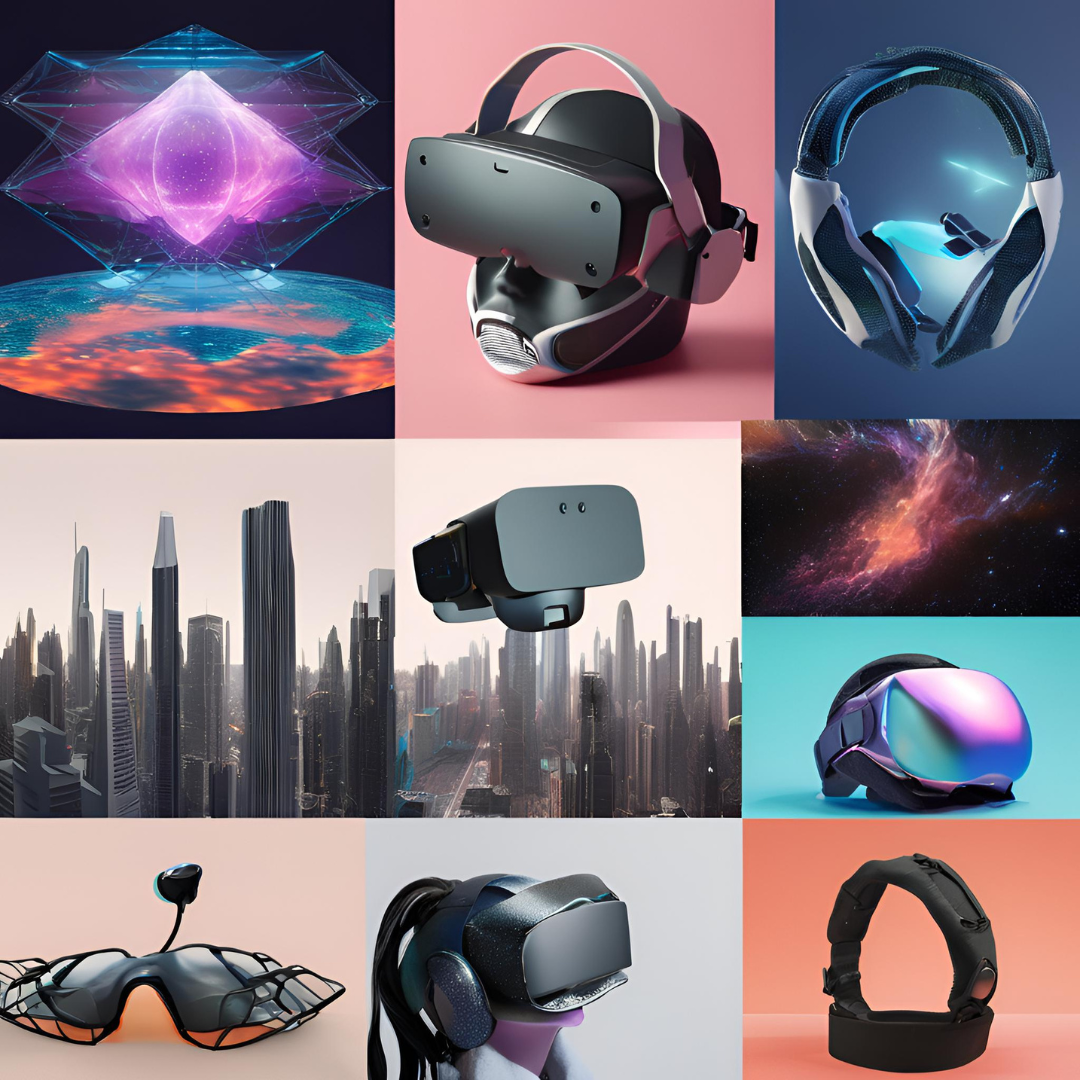
Current XR Trends Shaping Our Future
Based on my two decades in the field, here are the trends to watch:
- Lightweight, all-day wearable AR glasses
- Photorealistic mixed reality with perfect occlusion
- 5G-enabled cloud rendering for mobile XR
- Haptic feedback that feels real
- AI-driven virtual humans with natural interactions
The most exciting part? We're just getting started. The technology that seemed like science fiction during my first VR experience is becoming reality faster than even I expected. As someone who has dedicated their career to XR, I can tell you that the next five years will bring innovations that will make today's technology look as primitive as the Sword of Damocles seems to us now.
Lessons Learned and Looking Ahead
If there's one thing my journey in XR has taught me, it's that timing is everything. The technology was always promising, but it needed the right combination of hardware capability, software maturity, and market readiness to truly take off.
"The best way to predict the future is to create it." This quote has been my guiding principle throughout my XR journey, and it's never been more relevant than it is today.
As we stand on the brink of widespread XR adoption, I'm reminded of that first VR experience that sparked my passion. The wonder I felt then still drives me today, and I can't wait to see what the next chapter of XR evolution will bring.

Quest Lab Writer Team
This article was made live by Quest Lab Team of writers and expertise in field of searching and exploring
rich technological content in different fields and in different areas of the modern world